Trick or Treat: How Hackers Use Social Engineering to Gain Access

The Deceptive World of Social Engineering Social engineering attacks are some of the most effective tricks used by cybercriminals. By manipulating human emotions like trust, urgency, or fear, hackers deceive individuals into giving up confidential information or access to secure systems. From phishing emails to impersonating employees, these tactics allow criminals to bypass even the […]
End Users Are Your Last Line of Defense Against Cyber Criminals

If your business needs help with its cyber security, you’ve come to the right place for help.
Spear Phishing: Your Data at Risk

Phishing For Away In Spear phishing attacks are especially insidious. An attacker targets an employee in an attempt to trick him into releasing confidential data. These attackers may use your public directory to identify a likely target and send him an “urgent” request ostensibly from a higher-up. An employee who thinks he’s fulfilling a […]
Would One of These Social Media Scams Bamboozle You?

Social media can be a great business tool, but many scams can also utilize it. Read our blog to learn more.
Phishing is a Major Threat
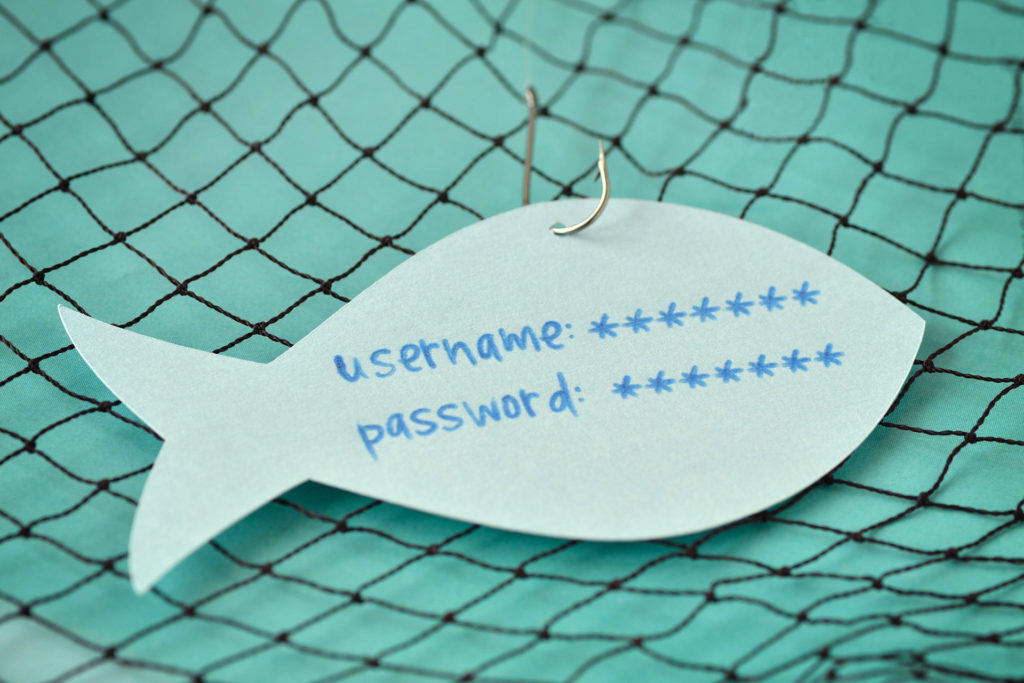
For this weeks’ tips we show you how to identify a phishing email. Visit our blog regularly for more great tips and tricks.






