Preparing Your Business for the 2024 Hurricane Season: What You Need to Know

As the 2024 hurricane season intensifies, it’s crucial for business leaders to stay informed and prepared. Colorado State University recently updated its forecast, predicting an even more active season than initially expected. With the National Hurricane Center’s forecasts and warnings readily available, there’s no better time than now to ensure your business is storm-ready. Updated […]
Hurricane Beryl: A Wake-Up Call for Business Preparedness in the 2024 Hurricane Season

This past weekend, Hurricane Beryl shattered records by becoming the first hurricane on record to reach Category 4 strength this early in the season. While projections suggest that Beryl will not pose a direct threat to the U.S., it serves as a stark reminder that the 2024 hurricane season is predicted to be highly unusual […]
Prepare Your Business for Hurricane Season: Atlantic Disturbance Updates and Key Precautions
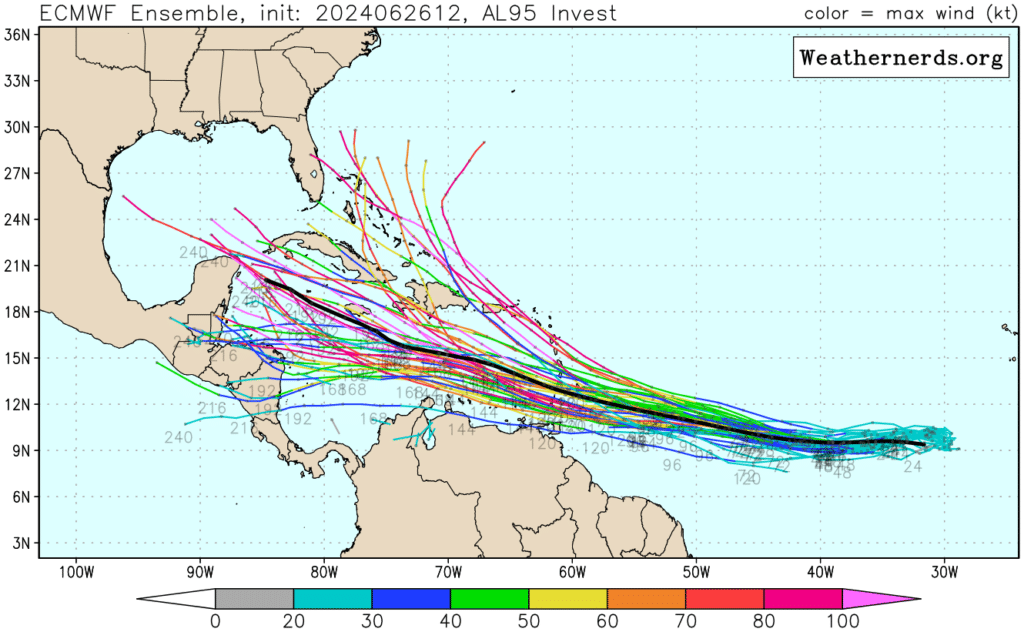
As the Atlantic hurricane season progresses, business leaders must remain vigilant and prepared. The National Hurricane Center (NHC) recently designated a tropical Atlantic disturbance, Invest 94L, as it moves through the Caribbean Sea. Another disturbance, Invest 95L, west of Africa, is also being closely monitored. Invest 94L is currently producing disorganized shower activity as it […]
Hurricane Season Starts Today – Is Your Business Protected?

As June 1 marks the official day hurricane season starts, business leaders must proactively protect their operations. The 2024 Atlantic hurricane season is predicted to be above normal, with an increased likelihood of more frequent and intense storms. According to the National Hurricane Center (NHC), this season could see 14-21 named storms, 6-10 hurricanes, and […]
Stay Prepared: NHC Tracking 3 Tropical Waves Just Days Before Hurricane Season
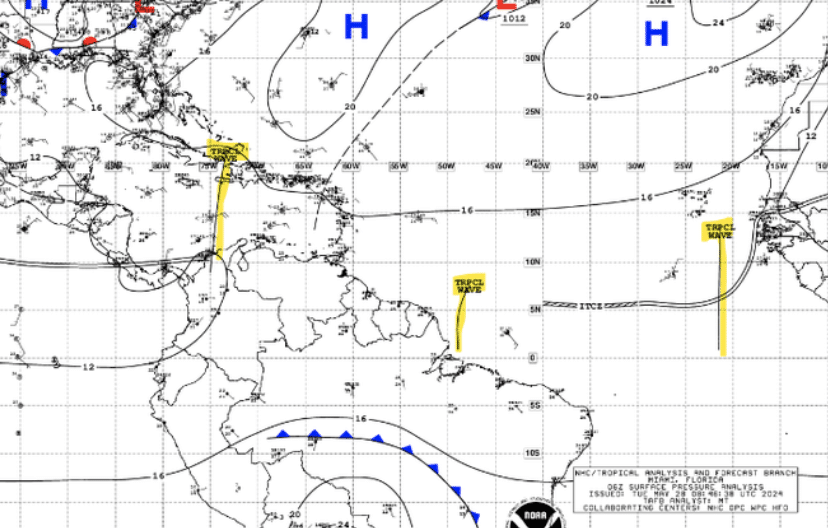
As the official start of the 2024 Atlantic Hurricane Season approaches, the National Hurricane Center (NHC) has already begun tracking three tropical waves. These disturbances are typical for this time of year and are the first we are seeing this season. One tropical wave is in the Caribbean, another near South America, and a third […]








